jEnigmaXIV

App details
About jEnigmaXIV
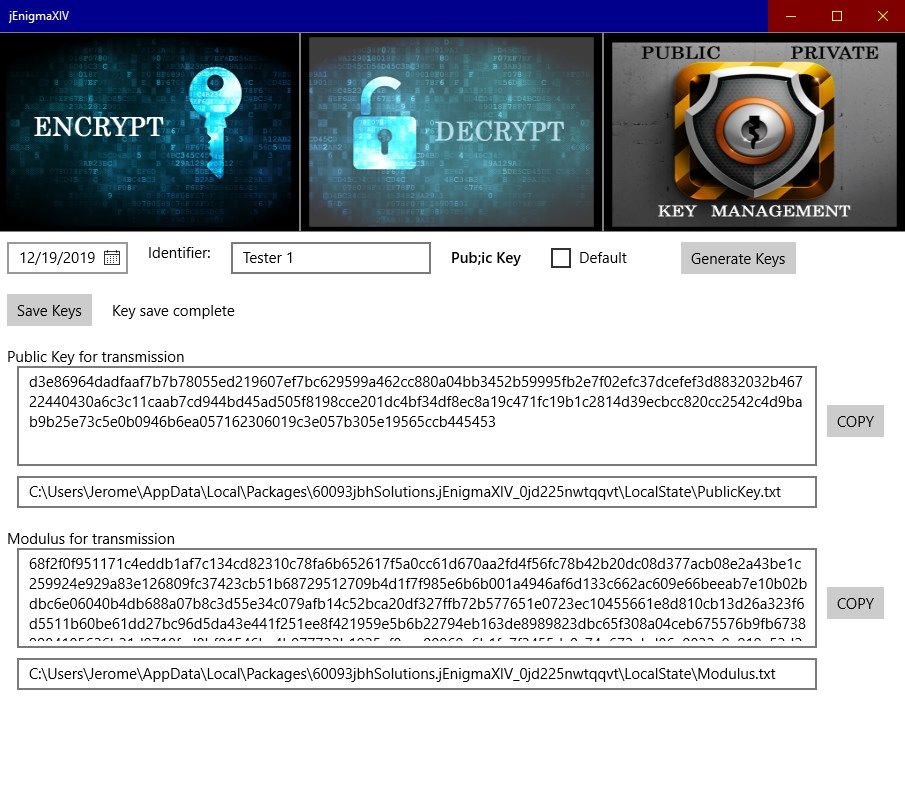
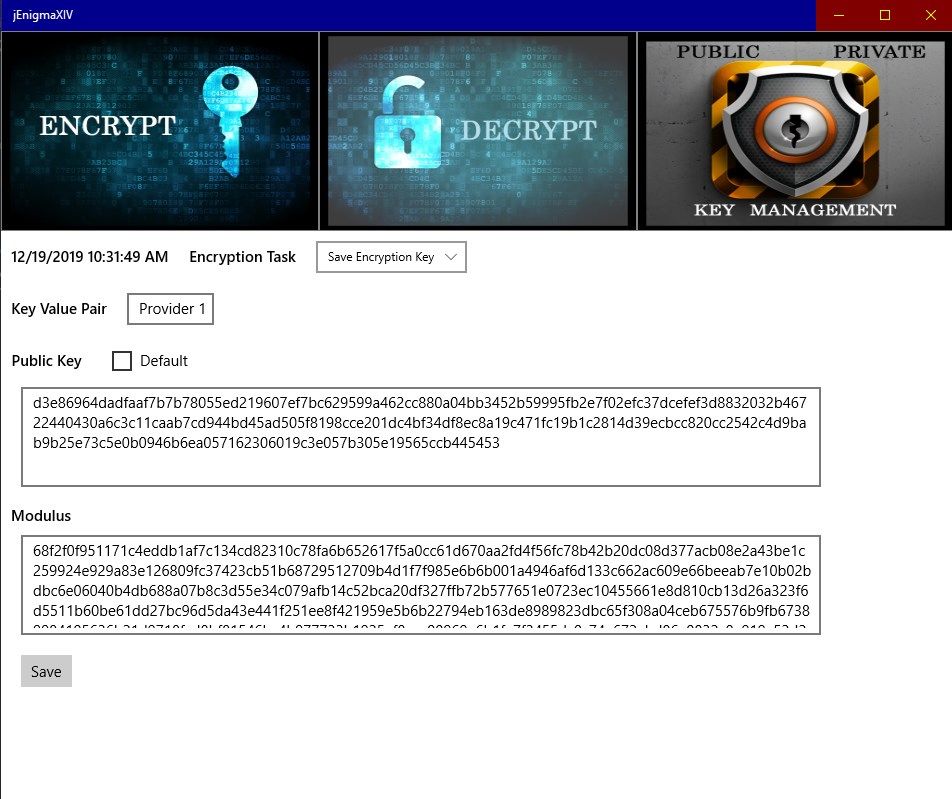
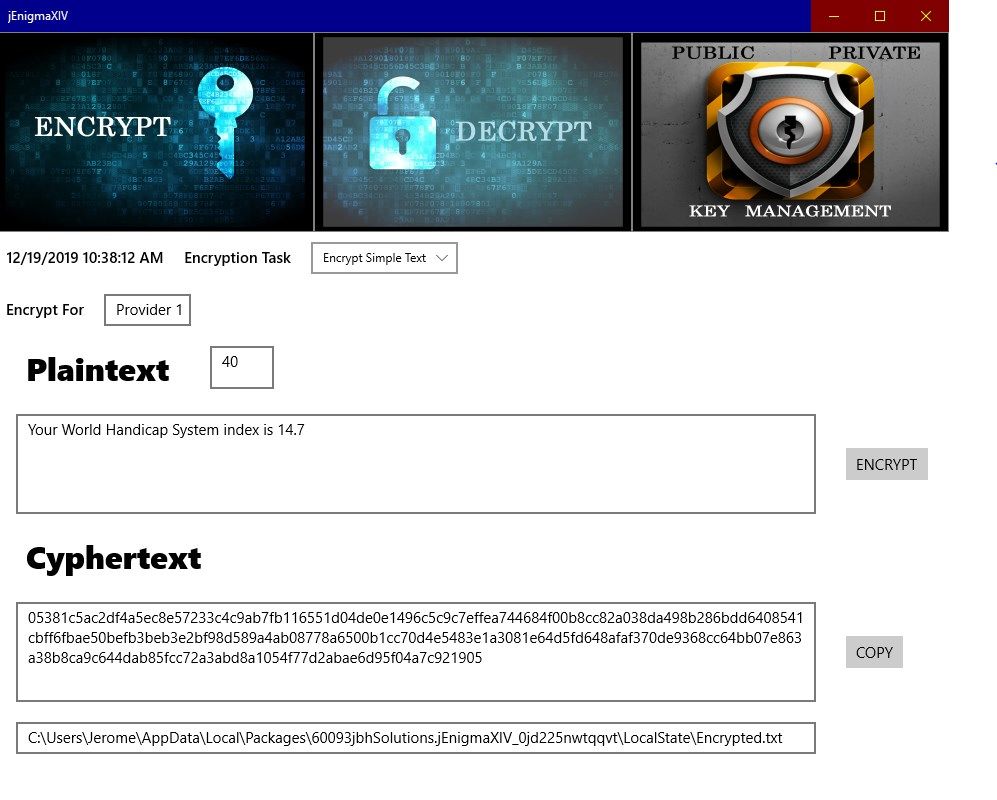
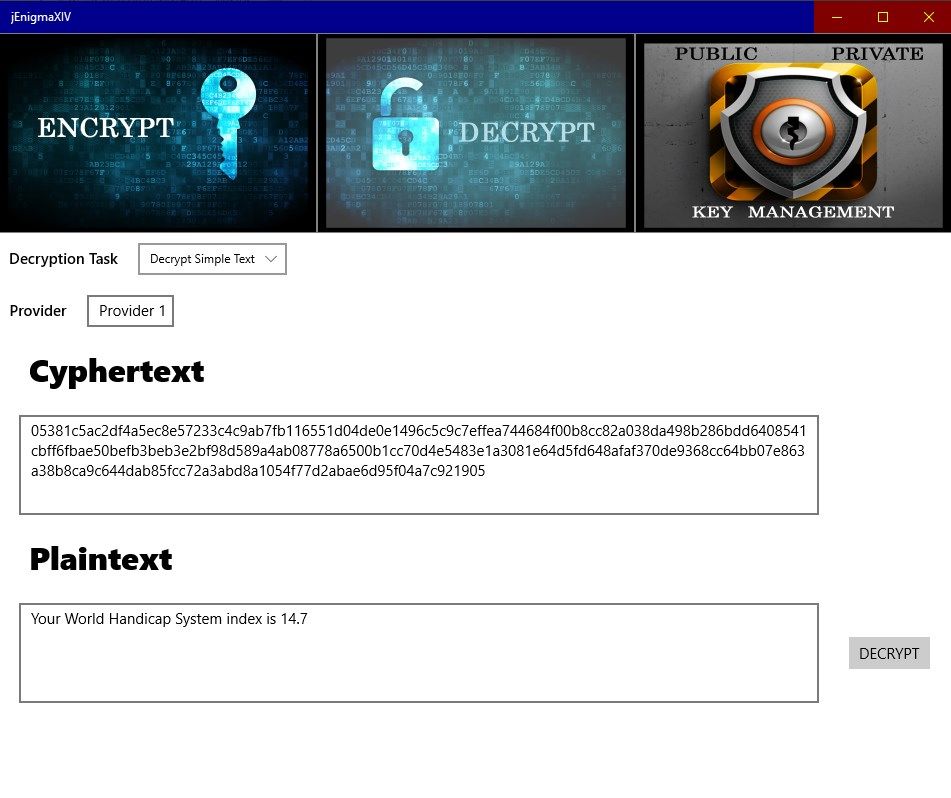
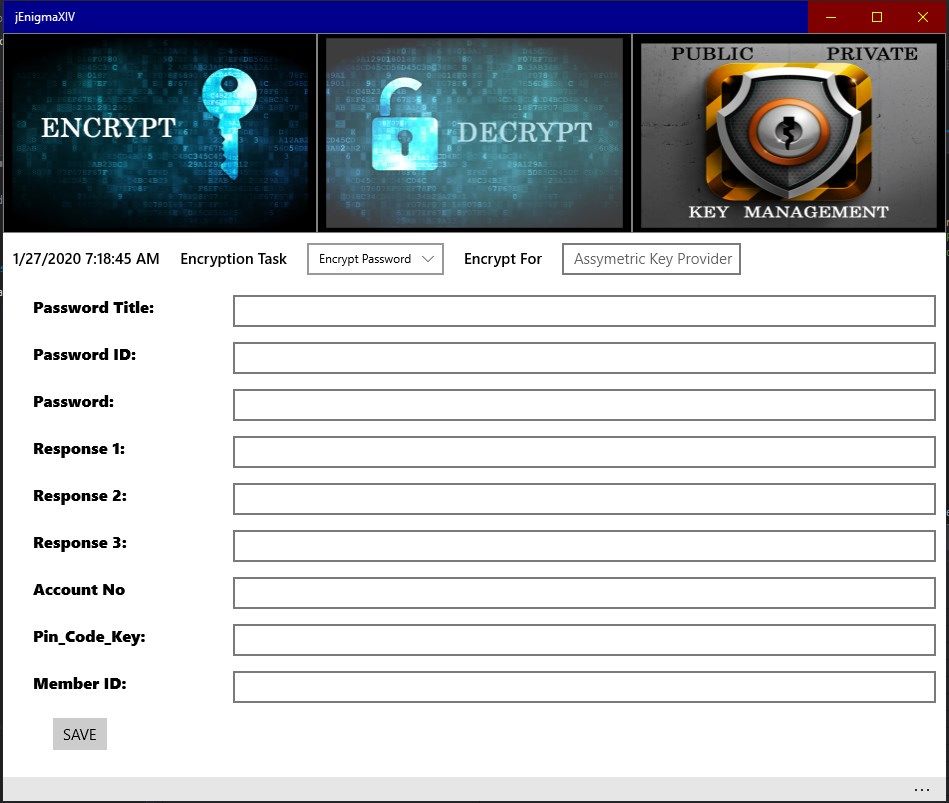
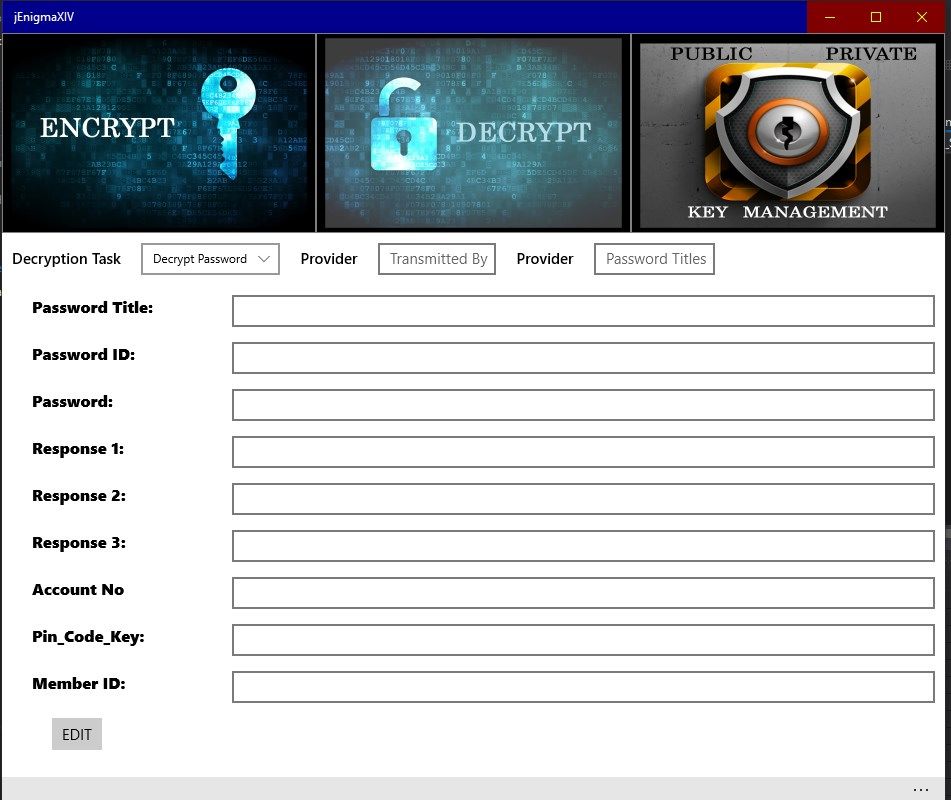
jEnigmaXIV is an asymmetric cryptology application to allow secure communication between two parties and for creating a secure encrypted database for user content. The application uses the public-private key methodology employed in RSA (Rivest–Shamir–Adleman) cryptosystems. The user has the option of creating a public key or relying on the applications default public key. The application randomly generates all facets needed for the RSA method using Big Integer methods (refer to the information provided in the app for acknowledgements). Public key and modulus text files are created for transmission to the party in which secure communication is to take place. The public key provider passes the key value pair to the second party through email. The receiver of the key value pair is required to download these files to the computer on which this app is loaded and drag /drop the files to their corresponding text boxes on the Encrypt page of the app for storage in a private database. The key value pair can then be used at any time to create a cypher text for trnasmission to the key value pair provider. Correspoindingly, the provider upon receiving the encrypted text file can drag/drop the file to the decrypt page to recover the plaintext message sent. Only simple text and block test files can be generated for transmission and will not be saved by the application. Secure encrypted data can only be saved on the key value pair generator computer and is the responsibiltiy of the user to maintain security of the data. Although reasonable care has been taken to ensure the correctness of this implementation, all liability and responsibility to any person or entity with respect to any loss or damage caused, or alleged to be caused, directly or indirectly, by the use of this application is disclaimed.
Key features
-
Text Encryption/Decryption